XID provides the following:
- Comparison between different data systems providing a report on account matching, duplicate and orphaned accounts
- Attribute level comparison with business rule injection to determine authoritative attribute anomalies
- Active Directory, LDAP and Unix group analysis for elevated privileged accounts
- Manager analysis identifying accounts without managers
- Rectification script generation giving the ability to bulk update attribute anomalies in systems
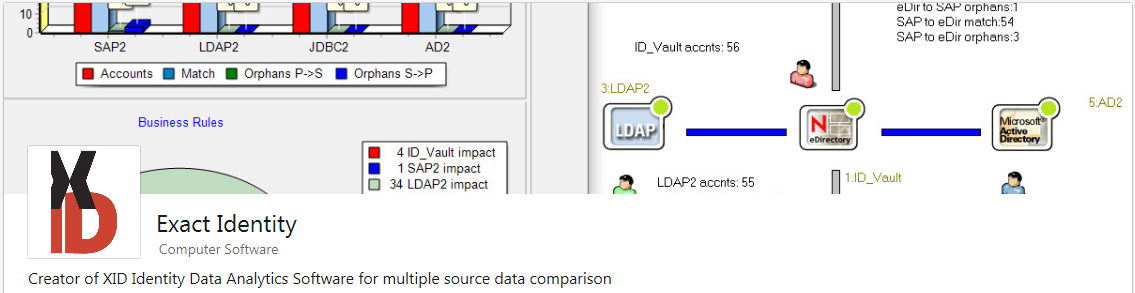
- Summary Report: Graphical report quantifying the anomalies found by the business analytics
- Detailed Report: Identifies each account and account attribute anomaly found
XID is Windows software and can run standalone from a network share, local hard drive or flash/USB drive. The software does not require any special hardware or support software to be installed.
Data anomalies are highlighted in a graphical summary report. A detailed report is generated and for the demo version, the first 10 anomalies from each system are shown.
XID can be downloaded and evaluated for free in demonstration mode*: download XID*
*In demonstration mode, detailed reports only show the first 10 anomalies per system. A full version password required to run without limitation..
For more information please email daren.roberts@exactidentity.com
XID Video
XID Screen Shots
XID Run Report - Project 1.
_________________________________________________________________________________
XID Summary Report.
_________________________________________________________________________________
XID Detailed Report.
_________________________________________________________________________________
XID Match Orphans.
_________________________________________________________________________________
XID Log.
_________________________________________________________________________________
XID Fix File for Project 1 LDAP Entity 1.
_________________________________________________________________________________
XID Run Report - Project 2.
_________________________________________________________________________________
XID Summary Report - Self.
_________________________________________________________________________________
Identity and Access Management:
We are targeting the product to be an essential part of the Identity Management professional and Data Analyst software toolkit so that early data issue resolution can begin right at the outset of a project.
Our solution is more collaborative than competitive to SailPoint/Oracle/Quest/CyberArk etc and was driven for the need to ensure data readiness was not an issue when the main IDM solution (SailPoint, Quest, NetIQ, Oracle, CyberArk, Microsoft etc.) goes live.
At the discovery phase of a project, XID can be active performing analytics on core data in scope for the IDM solution without the need to take data offsite or install hardware/extra software/databases etc.
XID can run from a PC local hard drive, network share or USB drive without the need to install any supporting software. The benefit of this is that the clients PC can be used without admin rights or modification.
Over time Identity Management data quality can be compromised which in turn can impact the security integrity of the Identity Management solution. XID can be used to periodically audit the data reporting data anomalies and providing business intelligence to regain security integrity.
Being able to analyse data deltas on a regular basis has the benefit of locating where the problems are being injected into the system. These issues can be corrected preventing repeated impact to the data that works against the automated systems being introduced.
If in the future new systems are to be integrated to the Identity Management system then XID can prepare this system for integration by checking data readiness of the system from a holistic perspective of the existing data estate.
XID is designed to analyze data at a fixed point in time. This is achieved by gathering extracts of data in LDIF, CSV or XML formats and creating a model on the production system. As data issues (once located) cannot be rectified in real time, there is limited benefit from reading or extracting the data in real time.
A reasonably current extract is sufficient when applying the concept of data issue resolution rendering which is analysis, identify issues, rectify issues then repeat the process until the data state is at an acceptable point of integrity. For this type of analysis and data issue resolution regime if is beneficial for XID to remain abstracted from production systems.
XID Identity and Access Management Benefits Summary:
- Designed to work stand alone or as a collaborative product to your existing IDM/IAM/IdAM solutions.
- Data integration is de-risked by providing a predictable outcome from the data integration simulation.
- Attribute and account level report information is provided from the simulation of data flow as per the Business rules and current data state.
- Data issue rectifications files are created based on authoritative data source rectification recommendations - e.g. XML/LDIF for LDAP/eDirectory/Active Directory, XML/CSV for database.
- Inconsistent data is reported such as duplicate identities, data inconsistencies, orphaned accounts and non-functional accounts that are deemed out of scope.
Data Migration:
For clients performing data migration, XID can analyse the data before and after migration comparing the resultant migrated data to a known baseline.
Other Data comparison tasks:XID can compare any data such as spreadsheet tabular or database data exported as CSV files for example; data from multi spreadsheets can be compared using XID and any data differences saved to a report.
XID market fit:
XID fits in any market where there is a need to have data analysed for one or many systems whereby business rules can be injected into the analysis process for information arbitration.
The value of XID to the customer is that it can predict success or failure of integrating data from an Identity Management perspective. Poor data quality can be an obstacle to completing a project on time or at all if issues arise from anomalies with this data.
Rapid repeatable data analysis expedites this process and alleviates the need to employ multiple analysts to perform analysis from the ground up with discrete electronic tools.
Project data readiness analysis can begin right at the outset, identifying data anomalies even before installation of the big vendor IDM/IAM solution. While many solutions have their own data analytics tools, often these tools cannot be utilised until the main product is installed which can take time. This time can be put to good use with XID, getting data ready so that the main IDM/IAM solution can get on with the task of managing Identities once installed and not rectifying data issues.
XID is enabler product for Identity Management projects. The product looks holistically at data in different systems and correlates merge points for data items common between systems.
Other benefits:
XID can be used by any Identity Management Professional or Data Analyst either as part of a consultancy or positioned within an organization for an Identity solution end user.
Results are obtained without any coding which allows any professional with good data knowledge to get up to speed.
XID is also a good fit for companies that have not yet implemented a big IAM solution but currently manage 'Identity Access Management' as a manual process.
XID can be downloaded and evalutated for free in demonstration mode.
*The XID full version software demonstration mode has the following limitations:
- Demo mode will expire quarterly.
- Detailed reports only show the first 10 anomalies per system.
- A full version password required to run without limitation... please contact us for more information
For more information please email daren.roberts@exactidentity.com
More information is available at the Exact Identity website: www.exactidentity.com
Other contact email info@automation.co.nz
All rights reserved. All other trademarks recognized. Copyright (c) 2014-2019 Exact Identity Limited.